AP News reports Apple to scan U.S. iPhones for images of child sexual abuse. When I first heard about this I thought, “This cannot possibly be true.” You mean, I take a photo of my 3-year-old daughter taking a bubble bath and upload it to the Cloud and Apple-deployed AI scans my phone to detect child porn and, if my account is flagged, a human being will look at my naked daughter and alert the authorities? “Apple unveiled plans to scan US iPhones for images of child sexual abuse, drawing applause from child protection groups.” So the answer is yes. That answer is horrifying and I do not find at all convincing AP News reassuring the reader that “[p]arents snapping innocent photos of a child in the bath presumably need not worry.” Presumably?
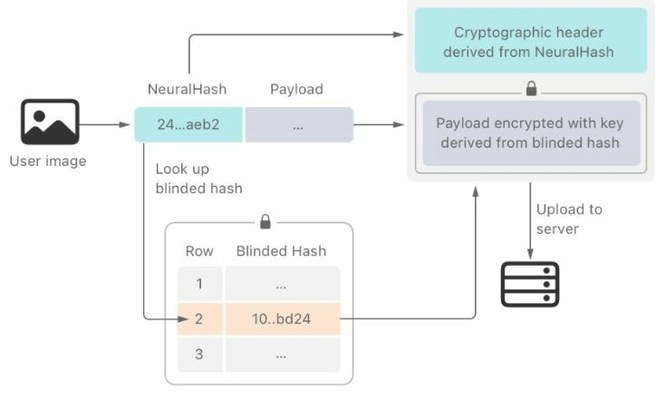
Apple’s tool designed to detect “known images of child sexual abuse” is called NeuralHash. It “will scan images before they are uploaded to iCloud,” AP News reports (emphasis mine). “If it finds a match, the image will be reviewed by a human. If child pornography is confirmed, the user’s account will be disabled and the National Center for Missing and Exploited Children notified.” The depth of surveillance doesn’t end there. “Separately, Apple plans to scan users’ encrypted messages for sexually explicit content as a child safety measure.” So if I engage in fantasy role-playing with others, an Apple-deployed program will scan my text and, if it sounds like child porn, then Apple turns me over to the authorities?
Not everybody AP News consulted for the story is applauding. “Matthew Green, a top cryptography researcher at Johns Hopkins University, warned that the system could be used to frame innocent people by sending them seemingly innocuous images designed to trigger matches for child pornography. That could fool Apple’s algorithm and alert law enforcement.” Green told AP News, “Researchers have been able to do this pretty easily.” In other words, Apple’s system can be manipulated to engage in a high-tech form of swatting. It is not hard to imagine corporate and state actors using this tactic to harass opponents by raising suspicions about them with law enforcement agencies. It’s not like the deep state hasn’t done things like this before.
* * *

USA Today is reporting that Dr. Anthony Fauci expects ‘a flood’ of COVID-19 vaccine mandates after full FDA approval. I have blogged about the problems surrounding this on Freedom and Reason (On the Ethics of Compulsory Vaccination; The Immorality of Vaccine Passports and the Demands of Nuremberg). What I want to draw attention to today is this myth Fauci repeats that this is a “pandemic of the unvaccinated.” This is a slogan designed to keep alive what is becoming quite obviously a counterproductive vaccine program. The evidence suggests that in fact it is the vaccinated who are prolonging the pandemic. Fauci knows as well as anybody that the vaccines are not efficacious in conferring immunity (only the virus can do that) and that the recent rise in cases (see above chart) is, at least in part, fueled by vaccinated people infected with SARS-CoV-2 exposing others to the virus.
Today, on Steve Bannon’s War Room: Pandemic, pathologist Dr. Kevin Homer provided a paradigm of what skepticism about all this should look like. CDC policy has Homer scratching his head. In the past, he explains, if a person had a virus, then one presumes he has developed immunity to the virus and therefore does not need a vaccine. Why expose a person who has survived a virus to the additional risks of a vaccine? If virus-acquired immunity was in question, tests can be be performed to confirm this. Gathering these data also provides facts for determining the extent of herd immunity. Moreover, as Dr. Robert Malone, the inventor of the mRNA platform, tells us, if you are healthy, there is no need to take the vaccine, as the risks of the vaccine outweigh the risks of the disease. (See “COVID-19 is Worse than the Flu”—For Whom? Will the Vaccinated Do the Right Thing and Mask Up or Stay Home?)
I have written about the risks these vaccines pose to human health (The Official Vaccine Narrative Completely Falls Apart). Perhaps the most risky thing about the mRNA platformed vaccines is the technology’s very mechanism of action, that is teaching cells to manufacture the spiked protein that causes COVID-19. The spike protein and a dysfunctional immune response to it lies at the root of the inflammation of the body’s organs and the problem of clotting blood associated with the advanced stage of the disease. This is why many vaccine recipients presents as a victim of long haul COVID-19. Since SARS-CoV-2 is not a sufficient condition to cause COVID-19, rather the spike protein is, indigenous production of the spike protein may prime the vaccinated for disease. Moreover, since the mRNA vaccines only teach the body this trick and do not confer immunity to the virus, those vaccinated with this technology are prone to become viral factories, endangering others.
“This is a dystopian world we’re living in,” Fauci remarked. As is his reflex, portraying the vaccine hesitant as ignorant and stupid, Fauci said if them that “they are being misled.” Certainly the public is being mislead. COVID-19 is a global propaganda operation. Ironically, standing outside the ideological bubble of progressivism tends to make one immune from the effects of the operation. The very people Fauci and other elites treat as irrational believers of rightwing conspiracy theories are the ones who are demonstrating the proper degree of skepticism. As for the hybristic progressive, elite propaganda portraying populist-nationalism as beyond the pale works best on those who put their political identity and virtue projection before the values they profess.
* * *
A tip to The National Pulse has unearthed an 21-page document from April 2017 entitled “9 Solutions to Secure America’s Elections” wherein a Biden-linked group, Center for American Progress, chaired by chief Democratic Party strategist John Podesta, and featuring Stacey Abrams, demands “robust” audits of elections. Why? Because of the wide array of problems associated with machine voting and the importance of election integrity in ensuring confidence in American democracy. Among other things, the Center for American Progress reveals that voting machines are hackable even without Internet access.

I encourage you to read The National Pulse article, but I want to share a few passages from the Center’s paper.
“Voting machines that record votes and tally them are run on software that is vulnerable to cyberintrusions. Well-resourced hackers, whether funded by foreign governments or criminal syndicates, have the access, ability, and motivation to infect computerized voting machines and tallying systems across America. This can occur even if the machines are not connected to the internet. Attackers, for example, can deploy software such as Stuxnet and Brutal Kangaroo to target offline voting machines.” The authors emphasize: “Even with strong chain-of-custody practices, hackers can remotely infiltrate an electronic machine’s operating system, and without paper-ballot records, it is impossible to know whether a hack occurred or if votes were changed.” Actually, this is not precisely true. It is more difficult. But there is a record of activity stored on the machines, which is why a forensic audit that includes inspection of machines is vital for ensuring election integrity.
“[The problem with electronic voting] is why there needs to be a paper ballot—which is software independent—for every vote cast. A paper ballot offers a record of voter intent, which will exist even if voting machines are attacked and data are altered. Paper ballots or records are necessary both to conduct meaningful postelection audits able to confirm the election outcomes, and to enable post-hoc correction in the event of malfunctions or security breaches.” That bit about enabling post-hoc correction is crucial. To translate, if an audit finds significant discrepancies, the vote should be corrected to reflect the will of the people. (Are you starting to wonder what changed between April 2017 and November 2020?)
“The utility of paper ballots and voter-verified paper records is only useful for ensuring that the outcome of an election is correct if election administrators commit to carrying out robust postelection audits,” the paper continues. “Many jurisdictions are not doing enough to conduct audits on an adequate number of ballots to ensure election accuracy and detect manipulation of vote totals caused by failing machines or hackers.” You will have noticed that, for example in Arizona, when Republicans organize an audit, they are attacked by Democrats and the corporate media for attempting to weaken the legitimacy of the 2020 election by calling into question the process. But only a few years before: “Given these facts, postelection audits—which are robust enough to create strong evidence that the outcome is accurate and to correct it if it is wrong—must be conducted after every election.”
The Center’s paper portrays Democrats as believing that election integrity is crucial to voter confidence in the democratic process. Yet, in 2020, because the correct outcome was secured, i.e., Donald Trump was removed from office, the story is not that confidence in the democratic process is undermined by election integrity. In hindsight, the paper seems not so much a plan of action for robust post-election audits, but instead instructions for how to steal an election. As several news sources have reported, Podesta played Joe Biden in an election war-game that took place ahead of the 2020 election, wherein he refused to concede defeat in the immediate aftermath of a clear Trump election-night victory. This was revealed in a report from the Soros-linked Transition Integrity Project.
According to reporting by Natalie Winters of The National Pulse, the D.C.-based Center for American Progress (CAP) has also repeatedly partnered with the China-United States Exchange Foundation (CUSEF) on sponsored trips to China and other endeavors for more than a decade. Podesta’s lobbying group recently employed Terry Neal, who subsequently worked to “provide strategic communications advice” for Huawei, a China-based technology company. Podesta’s brother, Tony, is also believed to be lobbying for Chinese Communist-linked tech giant Huawei. This is significant. The US government labels Huawei a “national security threat.” Huawei not only collaborates with the People’s Liberation Army, but provides the Chinese Communist Party backdoor access to its devices and networks.